Why Local Storage Is Non-Negotiable for Source Protection
The Cloud Exposure Problem
The Reporters Committee for Freedom of the Press operates a 24/7 legal hotline specifically because journalists face ongoing threats to their source materials from subpoenas, surveillance, and compelled disclosure (RCFP). When an investigative podcast producer stores research in a cloud service — Google Drive, Dropbox, Notion, or any hosted platform — that data is controlled by a third party subject to its own legal obligations. A subpoena served on the cloud provider can compel disclosure of the journalist's files without the journalist's knowledge or consent. The PRESS Act, which would bar federal law enforcement from gathering journalists' messaging and email records, has faced repeated legislative delays (EFF). Until federal shield protections are enacted, the legal exposure of cloud-stored research remains real.
The Freedom of the Press Foundation's 2026 digital security checklist for journalists recommends that reporters "take extra precautions to protect their sources and notes" in an environment of expanding government surveillance capabilities (Freedom of the Press Foundation). Their guidance emphasizes local encryption and air-gapped storage for sensitive materials. The Committee to Protect Journalists similarly advises that protecting confidential sources requires controlling where data resides physically, not only how it is encrypted in transit (CPJ).
For investigative podcast producers, the research itself is sensitive. The browsing patterns of an investigation reveal which public records were pulled, which names were searched, which addresses were investigated, and in what sequence. Even without reading the content, a third party with access to a producer's search history can reconstruct the shape of the investigation — and potentially identify the sources who pointed the producer toward specific records.
The Nieman Journalism Lab published 12 principles for protecting sources, emphasizing that journalists must control not only the content of their communications but the metadata — the records of who they contacted, when, and from where (Nieman Lab). Research metadata — which databases were queried, which names were searched, which pages were visited — is equally revealing. A cloud-stored research archive exposes this metadata to every entity that can compel the cloud provider to produce records.
How Local-Only Indexing Protects Sources
The structural advantage of local storage for source protection is straightforward: data that exists only on a machine the journalist physically controls cannot be obtained through a third-party subpoena. A court order directed at the journalist is a different legal situation — one where shield laws, the reporter's privilege, and legal representation come into play. But a subpoena served on Google or Dropbox bypasses all of those protections because the journalist is not a party to the demand.
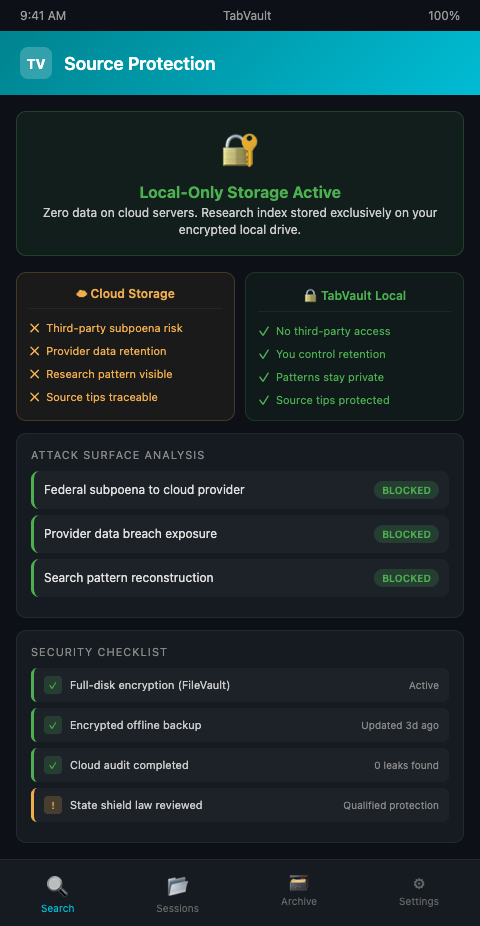
TabVault stores its entire search index on the producer's local machine, turning chaotic browser sessions into a searchable private database. No browsing data, indexed page content, or search queries pass through TabVault's servers or any cloud infrastructure. The private research database lives on the same hardware the producer physically controls — a laptop, a desktop, an encrypted external drive. This is what makes TabVault a non-cloud research storage journalist teams can rely on. Local storage source protection is not an added feature — it is the architectural foundation.
The practical implications are specific. When a producer researches a confidential source's tip by pulling county property records and corporate filings, TabVault indexes those pages locally. The source's tip led to specific searches, but the connection between the source and the research exists only in the producer's local index and in the producer's memory. No cloud service holds a record of which pages were visited, which searches were run, or which connections were discovered.
Consider the sequence. A source tells a producer to "look at the property records for 445 Oak Street." The producer pulls the county assessor page, the deed history, and the corporate filing for the LLC that owns the property. If those pages are indexed in a cloud-synced tool, a subpoena to the cloud provider reveals exactly what the source pointed the producer toward — the sequence of searches reconstructs the tip. If those pages are indexed locally in TabVault, the same subpoena yields nothing because there is no cloud provider in the chain. The source remains protected by the architecture of the tool, not by the producer's intention to protect them.
Source protection investigative podcast producers must treat as non-negotiable extends beyond the content of communications. It encompasses the metadata of the research process itself. The European Court of Human Rights established in Goodwin v. United Kingdom that protection of journalistic sources is a basic condition for press freedom — and that protection must extend to every vector through which a source could be identified, including research records that trace back to a source's original tip.
This matters most for investigations involving powerful subjects — public officials, corporations, law enforcement agencies — who have the legal resources to issue subpoenas and the motivation to identify sources. A producer investigating a county sheriff's department does not want the sheriff's attorneys to subpoena Google Drive and discover a folder of research organized by the names of officers who cooperated with the investigation. Local storage eliminates that vector entirely.
The distinction between local and cloud storage is not about paranoia — it is about attack surface. Every cloud service introduces a third party with its own legal obligations, its own data retention policies, and its own vulnerability to government requests. The ICIJ, which manages some of the most sensitive investigative data in journalism, built custom infrastructure specifically to keep source data off commercial cloud platforms (ICIJ). Most podcast producers cannot build custom infrastructure, but they can choose tools that store data locally rather than in the cloud. That choice alone eliminates the most common source-exposure vector for independent journalists.
TabVault's local-only architecture also aligns with the documentation standards that investigative producers need to maintain. The research audit trail exists — it is searchable and timestamped — but it exists under the producer's physical control, subject to the producer's decisions about disclosure.
The same local-privacy principle applies across investigative disciplines. Architectural salvage dealers protecting competitive sourcing intelligence use local browser indexing for the same structural reason: data that never leaves the local machine cannot be accessed by competitors, regulators, or third parties without the owner's knowledge.
Hardening Your Local Research Security
Encrypt the drive that holds the index. Local storage is only as secure as the hardware. Use full-disk encryption — FileVault on macOS, BitLocker on Windows, LUKS on Linux — so the TabVault index is unreadable if the machine is lost, stolen, or seized. The data filtering protocols you apply to your research should include filtering what data exists on unencrypted storage.
Maintain offline backups of the encrypted index. A local-only index is vulnerable to hardware failure. Back up the TabVault archive to an encrypted external drive stored in a physically secure location — a safe, a locked drawer, a safety deposit box. The backup should follow the same encryption standards as the primary drive.
Separate investigation indexes by sensitivity level. If some investigations involve confidential sources while others rely entirely on public records, maintain separate TabVault instances or session labels for each. This way, if one investigation's materials are ever subject to legal process, the producer can isolate the responsive archive without exposing unrelated investigations.
Audit your cloud footprint. Review every cloud service you currently use for research — Google Docs, Notion, Airtable, Trello, shared drives — and assess what investigation-related data each service holds. Migrate sensitive materials to local storage. Delete cloud copies of research that should not exist outside your physical control.
Know your state's shield law. Shield law protections vary dramatically by state. Some states provide absolute protection for confidential source materials; others provide qualified protection that can be overcome by showing need. The RCFP maintains a state-by-state guide to reporter's privilege protections. Your local storage strategy should be calibrated to the strength of your state's shield law — weaker shield protections demand stronger data security practices.
Conduct periodic access audits. Review who has physical access to the machines and drives where your TabVault index is stored. If a laptop is shared, if a home office is accessible to household members, or if an external drive is stored in an unsecured location, the local storage advantage is compromised. The private research database source safety model assumes physical custody — which requires conscious attention to the physical environment, not the digital one alone.
Plan for device seizure scenarios. If law enforcement seizes a laptop during an investigation-related search warrant, full-disk encryption protects the TabVault index from casual inspection, but a court order may compel decryption. Discuss device seizure protocols with legal counsel before they become relevant. The journalist data security local storage model is strongest when paired with legal preparation, so the producer knows their rights and response options before a seizure occurs.
Your Sources Trust You With Their Safety
Every confidential source who provides information to an investigative podcast producer is trusting that producer to protect them. Storing research in cloud services that respond to third-party subpoenas violates that trust, regardless of intent. TabVault gives investigative producers a private research database where source safety is architectural, not aspirational — no cloud servers, no third-party access, no data outside the producer's physical control. If you work with confidential sources, join the waitlist and start protecting them with the infrastructure they deserve.
A source tells you to check the property records for 445 Oak Street. You pull the county assessor page, the deed history, and the corporate filing for the LLC that owns the property. If those pages are indexed in a cloud-synced tool, a subpoena to the cloud provider reconstructs the exact sequence of your source's tip. With TabVault's local-only architecture, no cloud provider holds any record of which pages you visited or which connections you discovered. The source remains protected by infrastructure, not intention. Join the waitlist and give your confidential sources the architectural protection they deserve.